The hacking group LAPSUS$ is claiming responsibility for a major breach targeting AstraZeneca, one of the largest pharmaceutical companies in the world.
According to posts on hacker forums, the attackers say they stole roughly 3GB of internal company records.
AstraZeneca generates over $58.7 billion in annual revenue and employs around 90,000 people globally. If these claims hold up, the fallout could be severe for both the corporation and its workforce.
LAPSUS$ posted samples of the stolen files across multiple platforms, including its Telegram channel and dark web forums. The group is now trying to sell the full dataset to the highest bidder.
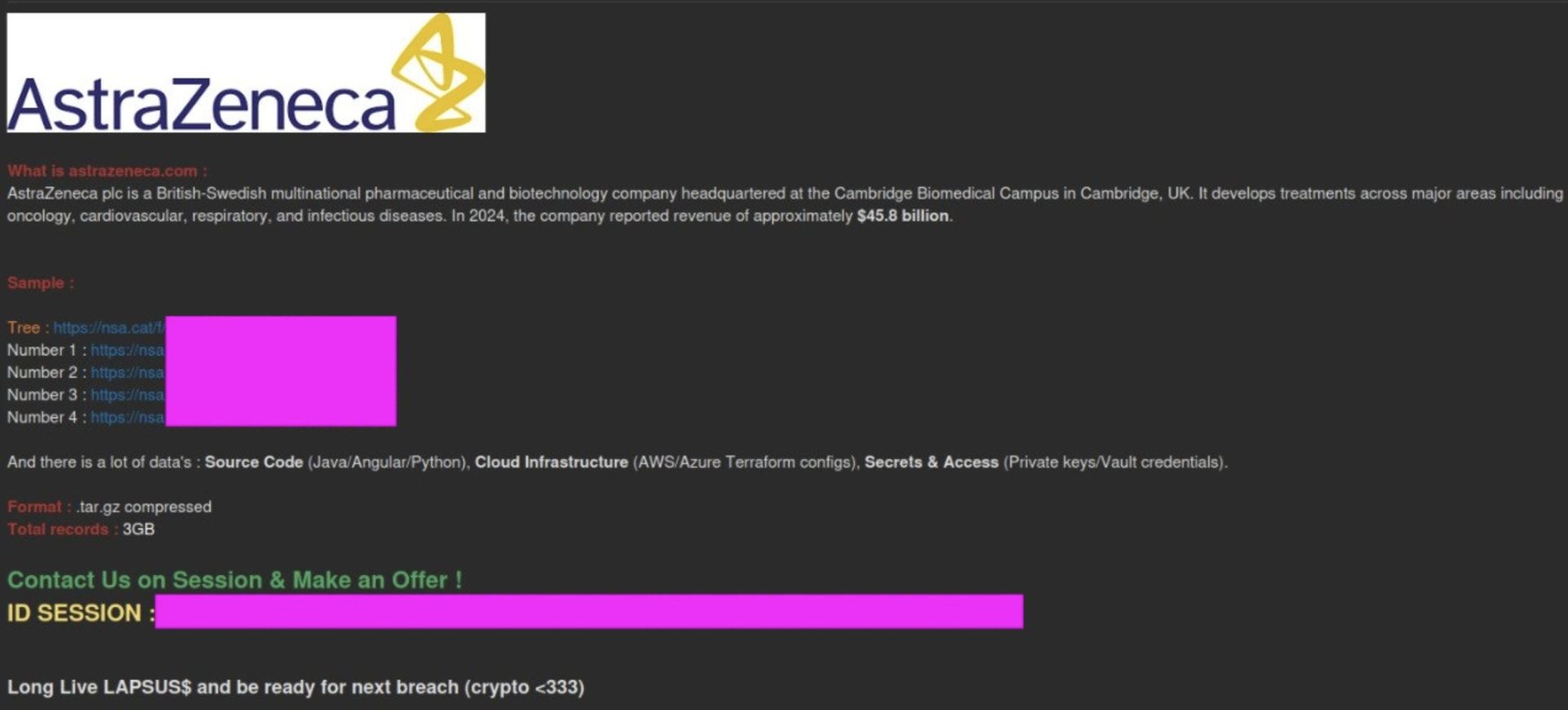
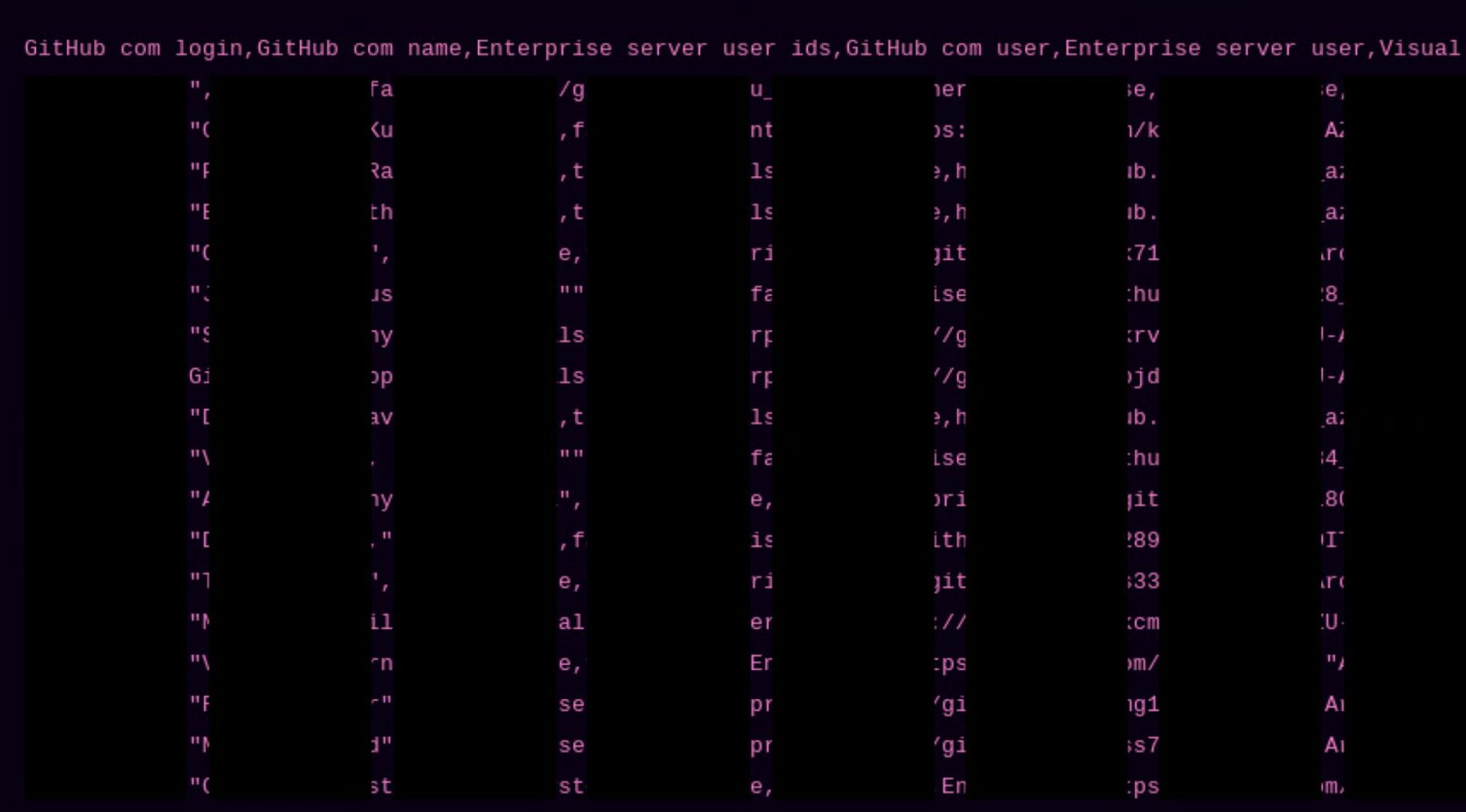
Security researchers reviewed the leaked samples and found that at least some records appear legitimate. Exposed information reportedly includes:
TROYPOINT Tip: Protect your identity and personal info from a data breach by using Aura Identity Theft Protection which is TROYPOINT’s recommended identity theft protection.
Aura Identity Theft Protection Review
At the time of writing, AstraZeneca has not confirmed or denied any incident. Multiple outlets have reached out for comment, but no official statement has been released.
LAPSUS$ first gained attention in 2022 after hitting targets like Okta, Nvidia, Samsung, and T-Mobile. Several members were later arrested in the UK, yet the group continues to surface with new claims.
Even though this incident targets a corporation rather than consumers directly, exposed employee and contractor records still put real people at risk. Stolen credentials and internal access logs can fuel phishing attacks along with identity fraud campaigns.
If your employer or a partner company suffers a similar event, take these steps right away:
This claimed attack on AstraZeneca is a reminder that no company, regardless of size, is immune to hackers.
Stolen source code and cloud keys are among the most dangerous types of exposed information because they open doors to deeper intrusions. Always review your own security habits and stay alert.
For more details on this story, refer to the report from Hackread.
We want to know your thoughts. What do you think about this story? Let us know in the comment section below!
Be sure to stay up-to-date with the latest streaming news, reviews, tips, and more by following the TROYPOINT Advisor with updates weekly.
This page includes affiliate links where TROYPOINT may receive a commission at no extra cost to you. Many times, visitors will receive a discount due to the special arrangements made for our fans. Learn more on my Affiliate Disclaimer page.

© IPTVSub is Proudly Owned by win-design