US-based food delivery platform GrubHub confirmed a data breach where hackers downloaded data from its systems.
The ShinyHunters cybercrime group is allegedly behind the attack. The hackers are now demanding Bitcoin payment to prevent releasing the stolen information.
GrubHub is one of at least 31 confirmed victims tied to a larger wave of Salesforce-related data thefts that prompted an FBI warning in September 2025.
The attackers didn’t hack GrubHub directly. They used stolen credentials from an August 2025 attack on Salesloft, a sales engagement platform that integrates with Salesforce.
Between August 8 and August 18, 2025, threat actors harvested OAuth tokens from Salesloft’s Salesforce integration. They used these tokens to infiltrate companies across multiple industries.
The stolen data reportedly includes:
GrubHub states that financial information and order history were not affected by this incident.
TROYPOINT Tip: Protect your identity and personal info from a data breach by using Aura Identity Theft Protection which is TROYPOINT’s recommended identity theft protection.
Aura Identity Theft Protection Review
GrubHub says it quickly investigated and stopped the unauthorized activity after discovering the breach. The company hired a third-party cybersecurity firm to assess the damage and has notified law enforcement.
The organization states it is taking steps to strengthen its security posture. GrubHub has not confirmed whether ransom negotiations with ShinyHunters are ongoing.
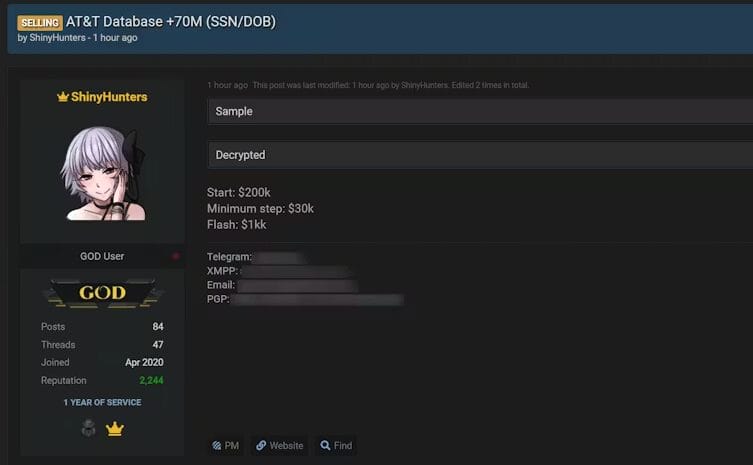
The ShinyHunters group is also allegedly responsible for data breaches involving Gucci, Gmail, AT&T, and several other organizations.
If you have a GrubHub account, take these steps now:
This GrubHub data breach shows how third-party integrations can become weak points in any company’s security. One compromised vendor exposed dozens of organizations in this attack wave.
Stay alert and review your account security settings regularly. Data breaches are becoming more common, and taking basic precautions now can save you serious headaches later.
For more details on this story, refer to the original report from BleepingComputer.
We want to know your thoughts. What do you think about this story? Let us know in the comment section below!
Be sure to stay up-to-date with the latest streaming news, reviews, tips, and more by following the TROYPOINT Advisor with updates weekly.
Your online activity is monitored by your ISP, app/addon/IPTV devs, government, and all websites.
🔒 Become anonymous while streaming & downloading with Surfshark VPN
Save 87% with 24-Month Plan + Get 3 FREE Months
Use on Unlimited Devices & Share 1 Account with Entire Family
CLAIM DEAL HERE
This page includes affiliate links where TROYPOINT may receive a commission at no extra cost to you. Many times, visitors will receive a discount due to the special arrangements made for our fans. Learn more on my Affiliate Disclaimer page.

© IPTVSub is Proudly Owned by win-design